19 Nov New Member: 3CORESec
3CORESec | Truth, Trust & Transparency
” We’re excited to announce that 3CORESec is joining the European Champions Alliance. The membership in ECA adds to 3CORESec’s belief on the power of communities and strategic partnerships as we feel that we should always strive to look toward continuous improvement.
From its early days the goal of collaboration has always been a building block for 3CORESec’s activities. Fun fact is that one of the first blog posts we made had the following statement:
We weren't happy with how things were going in information security so we decided to have our go at it. 3CORESec is on a mission to make information security transparent by developing platforms and services that are production-ready and buzzword free!
We have subsequently grown, matured and moved on, however this is still very much at the heart of what we do with the key goal of developing products and services for enterprise information security programs with a consistently evolving architecture, minimal footprint and full transparency of its capabilities and limitations. We even carry this in our company logo. In it you can distinguish three “T’s”, which stand for “Trust Through Transparency”.
We very much believe in investing, supporting and giving back to our community. Projects such as 3CORESec Blacklist help several European CERT’s as well as research programs on a daily basis. In addition, our open-source software assists detection engineers and threat hunters in the most demanding environments.
3CORESec recent open-source software releases:
- SIEGMA – SIEM consumable generator
- Automata – Automatic technical state compliance
- Trapdoor – A serverless honeytoken framework
Our partnership with ECA aims to increase the reach of these programs and assist in the development of the European technology and information security ecosystem. We’re looking forward to collaborating with other members of the Alliance as well as continuing our support of European-based research projects and organizations.”
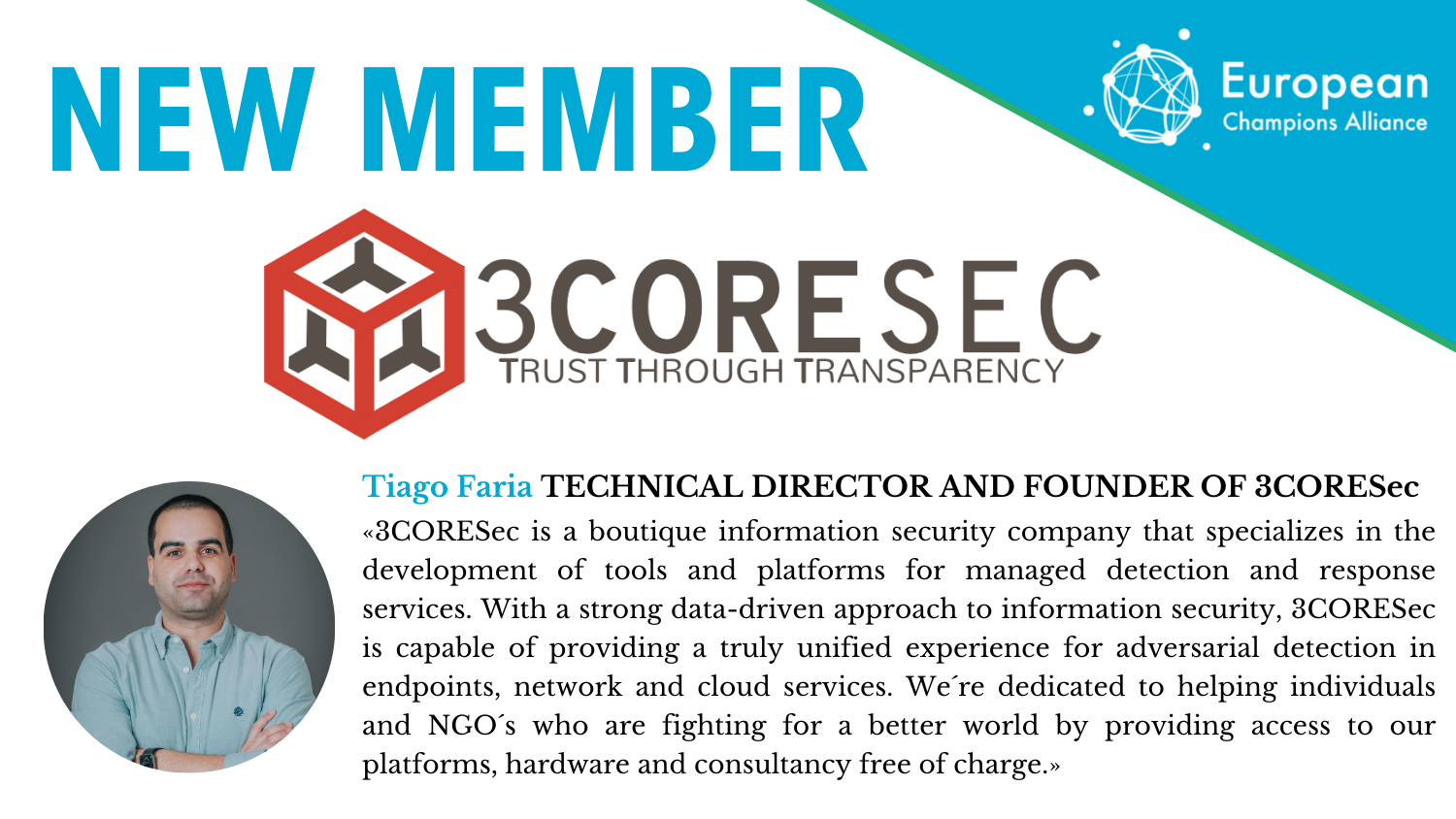
About 3CORESec
3CORESec was born out of the belief that information security threats require a unified and interoperable approach, which goes beyond the typical appliance and set and forget solutions. They specialise in the development of tools and platforms for threat hunting and detection of adversarial activity for cloud, endpoint and network-based threats.
Their base of operations is in Portugal with a team of developers spanning over 5 countries in the major time zones.
With a focus on original research and open-source software, 3CORESec has developed solutions such as the first SaaS platform for Network Intrusion Detection Systems (NIDS) management (lawmaker.cloud) as well as dtection.io, a European-operated threat detection rules and rulesets marketplace.
With a strong emphasis on automation their solutions are developed to equip people to do a better job of understanding the subtleties that are present in information security while automating the tasks that are better handled by systems. This commitment to automation allows their platforms to be implemented on companies of all sizes without the typical cost of information security solutions.
It is also their belief that automation and responsible use of open source can have a tremendous effect on both privacy and security, and that both of these should be available to everyone. Based on that belief, as part of 3CORESec’s ESG initiatives, they have created a social program in which they provide their services free of charge to any non-profit or NGO.
At the center of their technology is 3CORESec MDR – A managed detection and response platform that provides a unified and correlated approach to network, endpoint and cloud security. Equipped by their sophisticated SOAR platform their detection engineering is closely integrated with their orchestration playbooks for immediate and processual incident response.
Visit their website to learn more. Stay updated with the latest developments on their open source projects and contributions, community events or software releases by following them on Twitter. In the mood for technical write-ups? Visit their blog for articles on data-driven security, adversary emulation and cloud security or follow them on Linked:


